By Dr. David Barnett,
subject matter expert, brand monitoring Share this post



In part four of this series of posts looking at emerging internet content relating to coronavirus, we explore phishing.
In times of crisis, cyber criminals invariably take advantage of the growing concerns of the public. In the case of the coronavirus, they have done so by sending phishing emails that play on the fears surrounding the spread of the illness.
A number of reports have emerged of emails purporting to provide advice or assistance relating to COVID-19, but which are actually hooks to spread malicious content, or to drive people to websites intended to harvest personal details. Many of the phishing emails use the names of trusted organizations such as the World Health Organisation or the U.S. Center for Disease Control and Prevention (CDC) to add credibility to their content. A report published on March 20, 2020 stated that victims of online scams had lost £960,000 in coronavirus-linked cases since the start of February[1].
Some emails encourage the user to open an attachment that may contain malware. Identified cases include examples where attackers run code on a user’s computer or track their movements, steal information through keylogging, or lock files on the user’s device and demand a ransom for their reinstatement. Other instances have been reported of malicious files being distributed through copies of healthcare company or government agency websites[2],[3].
Some types of phishing emails drive users to lookalike websites intended to harvest login details; others directly solicit for payments. One particular case asked for Bitcoin donations, allegedly to aid the CDC in the search for a vaccine[4].
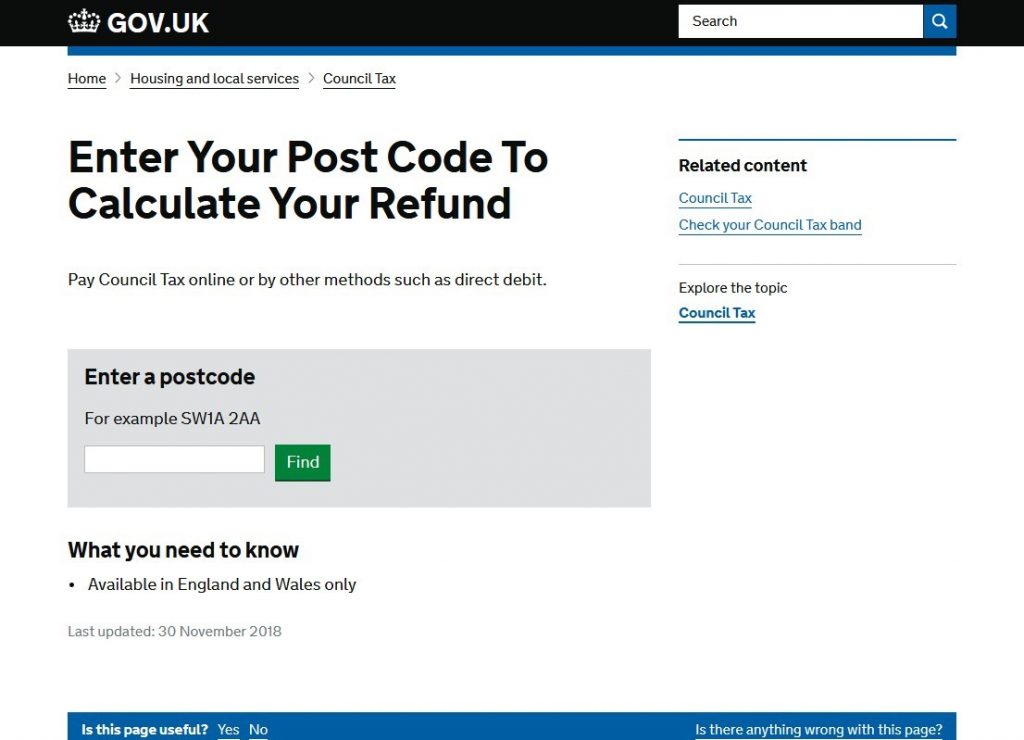
Fraudulent coronavirus communications may purport to provide benefits. One reported SMS-based scam offered free iPhones to encourage recipients to click a link to a fake site. Other reported scams include emails offering payday loans, tax rebates, insurance schemes or trading advice in response to the crisis, or offering products billed as coronavirus cures[5],[6].
Figure 1: Example of a fake government website hosted on a coronavirus-specific domain name, associated with a phishing scam using an SMS message offering a tax refund
As the crisis has progressed, there has been a rise in phishing activity over social media, typically involving fake accounts. Given the speed with which content can spread across social media—particularly in the current climate of fear—such scams have the potential to reach large numbers of people in a short time2.
How to keep your customers safe
It’s important to keep your customers, as well as your own employees, safe by making them aware of how to spot a phishing email. Tips for spotting phishing emails are generally the same as for most fraudulent campaigns. It may be a good idea to educate your customers as to what to expect from your company, and what a phishing scam may look like. Here are our tips for spotting a phishing email:
- Pay attention to the originating email address and the host domain of any embedded links; fraudsters may attempt to pass off their messages as being from a legitimate organisation (say, company.com) by using variants of the official domain name, such as company.org, or company-safety.com, in order to construct a convincing sender address. Even if an email appears to use the official domain name, it’s possible this information may have been spoofed.
- Hover over links without clicking them. Many fraudulent emails may show the legitimate domain in the visible link text while actually directing elsewhere. Bear in mind that even an email linking to an official site may incorporate a malicious attachment.
- Look out for anomalies in the email text. A phishing email could have:
- A generic rather than personalized greeting
- Spelling or grammatical mistakes
- Messaging that conveys a sense of urgency or has a deadline by when to act
- Other requests for personal information[7].
How CSC can help brand owners
CSC’s Anti-Phishing service can aid brand owners in detecting fraudulent emails and associated websites that may incorporate their branding illegally to add credibility. Our technology makes use of a combination of honeypot email accounts and other mail sources (i.e., customer abuse mailboxes, feeds from anti-fraud and security providers) to attract as large a cross-section of general spam traffic as possible to detect phishing emails. Emails are analysed and embedded links crawled to identify potentially fraudulent sites. We then use customer-specific rules to look for brand references and other associated keywords, in addition to comparing the fingerprint of the site against other known cases of fake content. When fraudulent content is detected—generally considered a contravention of terms and conditions by a number of internet service providers—we have a number of enforcement options to ensure the swift removal of the website.
If you’d like to find out more about our Anti-Phishing services, click here or fill in our online form to be contacted by one of our team.
[1] bbc.co.uk/news/uk-51964507
[2] mayerbrown.com/en/perspectives-events/publications/2020/03/dont-panic-stay-calm-legal-strategies-for-addressing-coronavirus-phishing-scams-in-hong-kong
[3] worldtrademarkreview.com/anti-counterfeiting/covid-19-phishing-warning-uspto-responds-wipo-election-microsoft-sued-news
[4] recordedfuture.com/coronavirus-panic-exploit/
[5] forbes.com/sites/mattperez/2020/03/16/coronavirus-scams-watch-out-for-these-efforts-to-exploit-the-pandemic/#443d4eaa6103
[6] news.sky.com/story/coronavirus-criminals-exploiting-covid-19-pandemic-with-email-scams-11959433
[7] https://us.norton.com/internetsecurity-online-scams-coronavirus-phishing-scams.html